- Quick Comparison of DDoS Protection Solutions
-
Top 20 DDoS Protection Solutions for 2026
- 1. Cloudflare DDoS Protection
- 2. Fastly DDoS Protection
- 3. Radware DDoS Protection
- 4. Imperva DDoS Protection
- 5. Akamai Prolexic
- 6. Azure DDoS Protection
- 7. Google Cloud Armor
- 8. AWS Shield
- 9. F5 Distributed Cloud DDoS Mitigation
- 10. A10 Defend DDoS Protection
- 11. Prophaze WAF
- 12. NETSCOUT Arbor Cloud
- 13. Oracle Web Application Firewall
- 14. Alibaba Cloud Web Application Firewall
- 15. Tencent Cloud Anti-DDoS Advanced
- 16. Nexusguard Application Protection
- 17. Gcore DDoS Protection
- 18. OVHcloud Anti-DDoS
- 19. Link11 DDoS Protection
- 20. Corero SmartWall ONE
- What DDoS Protection Solutions Are and Why They Matter
- Types of DDoS Attacks to Match With the Right Protection
- Core Capabilities to Compare in DDoS Protection Solutions
- Deployment Models for DDoS Protection
- How DDoS Mitigation Works From Detection to Recovery
-
How to Choose the Best DDoS Protection Solution
- 1. Match Protection Layers to Your Assets and Attack Risk
- 2. Compare Mitigation Capacity, Latency, and Global Coverage
- 3. Evaluate Automation, SLAs, Support, and Managed Response
- 4. Check Cloud, CDN, WAF, DNS, and SIEM Integrations
- 5. Consider Pricing Based on Clean Traffic, Protected Resources, and Attack Overages
- DDoS Protection Readiness Checklist Before an Attack
-
FAQ About DDoS Protection Solutions
- 1. What Is the Best Protection Against DDoS Attacks?
- 2. What Are the Best DDoS Protection Services?
- 3. Who Is the Leader in DDoS Protection?
- 4. Are DDoS Attacks Illegal in the United States?
- 5. Can a Firewall Stop a DDoS Attack?
- 6. How Do DDoS Protection Solutions Handle Legitimate Traffic During an Attack?
- 7. Do Small Businesses Need DDoS Protection?
- How 1Byte Helps Customers Build More Resilient Hosting Foundations
As 1Byte, we look at DDoS protection solutions the same way we look at power, routing, backups, and SSL: they are not optional decoration. They are availability infrastructure. Market overview: DDoS mitigation has moved from a niche security add-on into mainstream continuity spending, with researchers projecting the market to reach $10.39 billion by 2030.
The pressure is not theoretical. Cloudflare’s late-2025 reporting described a record-setting 31.4 Tbps DDoS attack, which tells us something blunt: attackers can now compress serious disruption into seconds. For a business, that means checkout failures, API timeouts, SLA credits, angry users, support floods, and a brand hit that outlives the traffic spike.
Quick Comparison of DDoS Protection Solutions
Use this table as a fast shortlist, not a final purchasing decision. We compare the first ten DDoS protection solutions by buyer fit, entry pricing style, evaluation path, and the limits most likely to surprise teams during procurement.
| Service/Tool | Best for | From price | Trial/Free | Key limits |
|---|---|---|---|---|
| Cloudflare DDoS Protection | Websites, SaaS, SMBs | Free plan | Permanent free tier | Advanced controls paid |
| Fastly DDoS Protection | APIs, edge apps | Usage-based | Free request tier | Request-metered |
| Radware DDoS Protection | Enterprises, hybrid networks | Custom quote | Trial by request | Sales-led sizing |
| Imperva DDoS Protection | Apps, APIs, compliance | Custom quote | Free trial | Trial bandwidth cap |
| Akamai Prolexic | Global enterprises | Custom quote | Demo-led | Routing prerequisites |
| Azure DDoS Protection | Azure workloads | Per IP or plan | Azure account | Azure-only scope |
| Google Cloud Armor | GCP apps, APIs | Pay as you go | Cloud credits | Load-balancer centric |
| AWS Shield | AWS-native teams | Included standard | Default standard tier | Advanced commitment |
| F5 Distributed Cloud DDoS Mitigation | Hybrid applications | Custom quote | Enterprise trial | Contract-led |
| A10 Defend DDoS Protection | ISPs, gaming, data centers | Custom quote | Demo by request | Capacity-based |
Top 20 DDoS Protection Solutions for 2026
We ranked these DDoS protection solutions for real buying situations: public websites, APIs, cloud-native apps, hybrid networks, service providers, gaming platforms, and regulated workloads. Our bias is practical. A good platform should block the attack, preserve legitimate traffic, give operators usable evidence, and avoid billing surprises.
1. Cloudflare DDoS Protection
Cloudflare is an edge-network and security company with large security engineering, reliability, and threat-intelligence teams. We see it as the default first serious move for many websites because it combines DNS, CDN, WAF, bot controls, and DDoS mitigation in one operational surface.
Best for: solo founders and SMB web teams that need quick protection without hiring a network security specialist.
- Always-on edge mitigation → absorbs common floods before origin CPU, memory, or bandwidth becomes the bottleneck.
- Rules, bot signals, and automation → saves roughly three to five manual firewall changes during a traffic spike.
- DNS-based onboarding → gives most small sites first value in about 15 to 45 minutes.
Pricing & limits: From $0/mo; trial length is a permanent free tier; clear caps include advanced bot management, deep logs, network-layer enterprise products, stronger support, and contractual SLAs on higher plans.
Honest drawbacks: The dashboard can feel crowded because Cloudflare sells many adjacent products. Also, advanced API security and enterprise network protection require a more serious commercial conversation.
Verdict: If you want a fast website defense layer, this helps you reduce origin exposure in the same afternoon. Beats most tools at speed-to-protection; trails specialist scrubbing providers on bespoke network engineering.
2. Fastly DDoS Protection
Fastly is an edge cloud company known for developer-friendly configuration, programmable delivery, and high-performance caching. Its security and platform teams appeal to engineers who want control rather than a black box.
Best for: platform engineers and API-heavy SaaS teams that already think in services, releases, and edge logic.
- Adaptive DDoS workflows → keeps APIs usable while filtering attack patterns near the edge.
- Edge logic and observability integrations → saves about two incident-room handoffs between developers and security teams.
- Self-service enablement → produces first value in about one hour for an existing Fastly property.
Pricing & limits: From $0/mo plus usage; trial length depends on account setup; clear caps include a request-metered free tier, separate pricing for WAF and bot capabilities, and package requirements for larger security bundles.
Honest drawbacks: Fastly rewards teams that understand edge configuration. Smaller marketing-led websites may prefer Cloudflare’s simpler path.
Verdict: If you ship APIs and need engineering-grade visibility, this helps you protect app traffic without surrendering edge control in the first implementation sprint.
3. Radware DDoS Protection
Radware is a long-running application delivery and cybersecurity vendor with a deep DDoS research, emergency response, and hybrid-defense culture. We like Radware when the buyer has real network risk, not just a brochure requirement.
Best for: enterprise SOC teams and financial-services infrastructure teams that need cloud, on-premises, or hybrid DDoS mitigation.
- Behavioral DDoS detection → catches bursts and protocol abuse before static thresholds become useful.
- Managed response and automation → saves roughly 15 to 30 minutes of manual escalation during high-pressure incidents.
- Cloud or hybrid deployment → gives first operational value after baseline, routing, and runbook setup.
Pricing & limits: From custom quote/mo; trial length is available by request; clear caps depend on protected infrastructure size, traffic volume, managed service level, cloud versus appliance deployment, and web DDoS add-ons.
Honest drawbacks: It is not a casual small-site purchase. Procurement, tuning, and runbook alignment take planning.
Verdict: If you run critical infrastructure and need mature mitigation playbooks, this helps you reduce attack impact within a disciplined security program.
4. Imperva DDoS Protection
Imperva, now part of Thales, brings application security, WAF, API protection, bot management, and DDoS defense into one platform. Its team strength is especially visible where security, compliance, and application availability overlap.
Best for: ecommerce security teams and healthcare SaaS operators that need WAF plus DDoS coverage.
- Application and network DDoS protection → keeps public apps reachable while attacks shift across layers.
- WAF, bot, API, and DDoS integration → saves about four policy-review steps across separate tools.
- Self-onboarding for web assets → gives first value in about one business day for standard web properties.
Pricing & limits: From custom quote/mo; trial length is 30 days; clear caps include a trial bandwidth limit, production sizing by IPs, networks, DNS zones, protected applications, and add-on modules.
Honest drawbacks: Pricing transparency is limited before sales engagement. Teams that only need basic L3/L4 protection may find the broader application-security bundle more than they need.
Verdict: If you need DDoS defense tied to application security, this helps you protect revenue paths and compliance-sensitive apps quickly.
5. Akamai Prolexic

Akamai is one of the most established names in global edge delivery and security. Prolexic is its specialist DDoS platform, backed by security operations teams that understand carrier-scale routing, scrubbing, and incident coordination.
Best for: large enterprises and global SaaS providers with public prefixes, data centers, hybrid cloud, and strict uptime obligations.
- Dedicated scrubbing and edge controls → protects infrastructure before dirty traffic reaches firewalls or load balancers.
- SOCC-backed routing automation → saves roughly one full incident bridge cycle during major attacks.
- Always-on or on-demand models → gives first value after prefix validation, routing tests, and runbook rehearsal.
Pricing & limits: From custom quote/mo; trial length is not published for open self-service; clear caps include routing requirements, eligible prefixes, GRE or direct connectivity design, support tier, and managed response scope.
Honest drawbacks: Prolexic is enterprise infrastructure, not a plug-in. Buyers need network engineering maturity and budget discipline.
Verdict: If your business cannot tolerate network-edge collapse, this helps you keep critical services reachable during large attacks.
6. Azure DDoS Protection
Azure DDoS Protection is Microsoft’s native DDoS service for Azure resources. Its product and cloud network teams design it for virtual networks, public IPs, telemetry, and direct Microsoft support during attack events.
Best for: Azure-native platform teams and regulated SMBs protecting public IP workloads in Microsoft cloud.
- IP and network protection tiers → maps protection to either specific public IPs or wider virtual-network estates.
- Native Azure telemetry and response → saves roughly three portal-to-SIEM lookup steps during triage.
- Portal-based enablement → gives first value in about 30 to 60 minutes for known Azure assets.
Pricing & limits: From $199/mo per protected public IP; trial length is not a dedicated DDoS trial; clear caps include Azure resource scope, a higher-cost network plan for broader estates, and billing that begins when protection is enabled.
Honest drawbacks: It is best inside Azure. Multi-cloud teams still need a broader edge or scrubbing strategy.
Verdict: If your exposed workloads already live in Azure, this helps you add cloud-native mitigation and attack visibility without changing providers.
7. Google Cloud Armor
Google Cloud Armor is Google Cloud’s WAF and DDoS protection layer around supported Google load-balancing and edge architectures. The product team focuses on policy enforcement, adaptive protection, and GCP-native deployment patterns.
Best for: GCP platform engineers and API teams using Google load balancers, Cloud CDN, or internet-facing services.
- Security policies at Google’s edge → blocks abusive HTTP traffic before backend services scale unnecessarily.
- Adaptive protection and policy automation → saves about two to four manual rule-writing steps during L7 anomalies.
- Console and Terraform workflows → gives first value in about one to two hours for teams already on GCP.
Pricing & limits: From about $5/mo per standard policy plus rule and request charges; trial length can use Google Cloud trial credits for eligible usage; clear caps include protected-resource counting, data-processing fees on enterprise tiers, and load-balancer dependency.
Honest drawbacks: Cloud Armor is elegant inside Google Cloud but less natural for arbitrary external origins. Cost modeling matters when request volumes surge.
Verdict: If you build on GCP, this helps you protect apps and APIs while keeping security policy close to your cloud deployment pipeline.
8. AWS Shield
AWS Shield is Amazon Web Services’ managed DDoS protection family. The standard tier is automatic for many AWS services, while Shield Advanced adds deeper visibility, cost protection eligibility, and response-team access.
Best for: AWS-native startups and enterprise cloud teams running CloudFront, Route 53, Elastic Load Balancing, EC2, or Global Accelerator.
- Default network protection → reduces exposure to common L3/L4 attacks without extra deployment work.
- Advanced DRT and WAF coupling → saves about one escalation path between cloud ops and security during attacks.
- Resource-level enablement → gives first value in under an hour for eligible AWS resources.
Pricing & limits: From $0/mo for Shield Standard; Shield Advanced starts at $3,000/mo plus eligible data-transfer usage; trial length is not an open trial; clear caps include eligible AWS resources, support-plan expectations, and a one-year Advanced commitment.
Honest drawbacks: Shield Advanced is expensive for small workloads. Also, non-AWS assets need separate protection.
Verdict: If you are committed to AWS and need stronger DDoS guarantees, this helps you reduce both outage risk and attack-related cost shock.
9. F5 Distributed Cloud DDoS Mitigation
F5 has decades of application delivery and security experience, and its Distributed Cloud team now brings that heritage into SaaS-delivered security, multi-cloud networking, and managed DDoS mitigation.
Best for: hybrid application teams and existing F5 customers that want L3 through L7 protection with managed support.
- Always Available and Always On options → matches standby scrubbing or continuously routed protection to business risk.
- SOC, API, SIEM, and automation integrations → saves roughly three response steps across network, app, and security teams.
- Managed onboarding → gives first value after service design, routing validation, and attack procedure setup.
Pricing & limits: From custom quote/mo; trial length is available as an enterprise trial by request; clear caps depend on subscription model, protected bandwidth, support level, deployment mode, and managed-service scope.
Honest drawbacks: It can feel heavyweight for a single public website. The strongest fit appears when F5 is already part of the architecture.
Verdict: If you need app and network protection across hybrid estates, this helps you standardize mitigation without rebuilding every ingress path.
10. A10 Defend DDoS Protection
A10 Networks builds high-performance application delivery and network security products. A10 Defend is especially relevant for service providers, data centers, and gaming platforms where traffic volume and packet rate matter.
Best for: ISPs, hosting providers, gaming operators, and network teams that want appliance, virtual, or hybrid-style control.
- High-throughput DDoS mitigation → filters floods close to the network edge before customer services degrade.
- Threat intelligence and orchestration → saves about 10 to 20 minutes of manual blocklist and policy updates.
- Capacity-planned deployment → gives first value after traffic baselining and appliance or virtual instance rollout.
Pricing & limits: From custom quote/mo; trial length is demo-led and not standardized publicly; clear caps depend on appliance model, throughput, packets per second, modules, support, and intelligence services.
Honest drawbacks: A10 is not the easiest route for non-network teams. It fits buyers who can size, operate, and monitor serious infrastructure.
Verdict: If you run networks for others, this helps you turn DDoS defense into a controlled, measurable service capability.
11. Prophaze WAF
Prophaze is a web application and API security provider with emphasis on AI-driven WAF, Kubernetes protection, bot mitigation, and application-layer DDoS defense. Its team speaks naturally to DevSecOps and cloud-native buyers.
Best for: Kubernetes teams and SMB application owners that need WAF, API, bot, and L7 DDoS protection together.
- AI WAF and L7 DDoS controls → reduces abusive request pressure before apps waste compute on fake users.
- Kubernetes and hybrid deployment options → saves roughly three separate ingress-security configuration steps.
- Guided onboarding flow → gives first value in about 15 minutes for straightforward web assets.
Pricing & limits: From $0/mo on the basic free plan; trial length is 15 days for evaluation paths; clear caps include one free-domain style entry point, paid domain/subdomain expansion, deployment model, and traffic profile.
Honest drawbacks: Prophaze is strongest at application-layer protection, not carrier-scale backbone scrubbing. Very large enterprises may require deeper commercial validation.
Verdict: If your pain is HTTP abuse, API scraping, and bot-driven floods, this helps you harden the application edge within days.
12. NETSCOUT Arbor Cloud
NETSCOUT Arbor Cloud comes from a company deeply embedded in network visibility, service-provider telemetry, and DDoS threat intelligence. Its team strength is carrier-grade detection, hybrid mitigation, and 24/7 security operations.
Best for: telecom providers and enterprises that want cloud scrubbing plus on-premises detection or edge defense.
- Hybrid Arbor architecture → catches state-exhaustion and volumetric attacks across local and cloud layers.
- ATLAS-backed intelligence and SOC support → saves about one full manual escalation path during major events.
- BGP or DNS diversion model → gives first value after routing, signaling, and clean-traffic return testing.
Pricing & limits: From custom quote/mo; trial length is not publicly listed as self-service; clear caps depend on protected bandwidth, scrubbing model, Arbor Edge Defense use, service tier, and deployment geography.
Honest drawbacks: Some buyers may find the platform more network-operations oriented than app-security oriented. It also requires serious onboarding coordination.
Verdict: If your risk lives at the network edge, this helps you protect large pipes and critical services with mature operational support.
13. Oracle Web Application Firewall
Oracle Web Application Firewall is part of Oracle Cloud Infrastructure’s security portfolio. Oracle’s cloud security team positions it around OCI workloads, load balancers, SaaS protection, OWASP rules, bot controls, and L7 DDoS reduction.
Best for: OCI customers and Oracle application teams that want native WAF and application-layer protection.
- Edge and load-balancer WAF enforcement → blocks malicious web traffic before it reaches application servers.
- Threat intelligence and bot checks → saves about two to three manual access-control updates per incident.
- OCI-native policy setup → gives first value in about one to two hours for existing OCI load-balanced apps.
Pricing & limits: From $0/mo for the first eligible WAF instance and included request allowance; trial length follows Oracle Cloud Free Tier or account evaluation; clear caps include request volume, instance count, load-balancer design, and regional service availability.
Honest drawbacks: This is not a full replacement for dedicated L3/L4 scrubbing. Non-OCI teams may prefer a cloud-neutral edge provider.
Verdict: If your applications already sit on OCI, this helps you add WAF and L7 DDoS resilience without leaving Oracle’s control plane.
14. Alibaba Cloud Web Application Firewall
Alibaba Cloud WAF protects web applications and APIs, with particular relevance for organizations serving China, Southeast Asia, and cross-border ecommerce markets. Its cloud security teams understand regional traffic, compliance, and high-volume retail patterns.
Best for: APAC ecommerce teams and businesses that need protection close to Alibaba Cloud-hosted workloads.
- Managed WAF and web DDoS filtering → reduces malicious requests before they overload origin applications.
- Cloud security suite integrations → saves roughly two procurement steps when buyers already use Alibaba Cloud security tools.
- Console-driven setup → gives first value in about one business day for standard web onboarding.
Pricing & limits: From $1.60/mo promotional entry pricing for new users where available; trial length and discounts vary by region and campaign; clear caps include edition, domain count, QPS, traffic, bot controls, and DDoS add-ons.
Honest drawbacks: Global buyers must check region, compliance, support language, and cross-border latency carefully. Pricing can be promotion-sensitive.
Verdict: If your growth depends on APAC reach, this helps you protect regional web traffic while staying inside Alibaba Cloud’s ecosystem.
15. Tencent Cloud Anti-DDoS Advanced
Tencent Cloud Anti-DDoS Advanced is built for high-traffic internet businesses, especially gaming, media, finance, and China-facing digital services. Tencent’s security and cloud network teams bring strong experience with real-time traffic and attack cleaning.
Best for: online gaming operators and China-facing application teams that need high-defense IP protection.
- High-defense proxy IP model → hides real servers and absorbs network, transport, and application-layer attacks.
- AI cleaning and elastic protection → saves about three manual scaling decisions during attack peaks.
- Policy-based portal operations → gives first value after DNS, forwarding, and protected-port configuration.
Pricing & limits: From custom quote/mo or postpaid billing by plan; trial length is not a standard public trial; clear caps include base protection bandwidth, business bandwidth, forwarding rules, elastic bandwidth, daily peak billing, and region.
Honest drawbacks: Billing design takes attention. Teams unfamiliar with base versus elastic protection can misread the economics.
Verdict: If low-latency regional availability matters, this helps you keep real-time services online while shielding origin infrastructure.
16. Nexusguard Application Protection

Nexusguard focuses on DDoS mitigation, application protection, and service-provider enablement. Its team combines cloud scrubbing, bastion-style deployment, WAF protection, reporting, and partner-friendly managed security models.
Best for: ISPs, system integrators, and high-risk website operators that need managed DDoS plus WAF.
- Always-on DDoS and WAF layering → filters volumetric and web threats before they reach public-facing apps.
- Threat intelligence and event notifications → saves about two to three monitoring hops through email, syslog, or SNMP workflows.
- Managed cloud or hybrid onboarding → gives first value after protected-IP, DNS, or routing setup.
Pricing & limits: From custom quote/mo; trial length is not public self-service; clear caps depend on protected IP addresses, protection level, traffic size, support model, and partner or franchise arrangement.
Honest drawbacks: Buyers looking for transparent swipe-card pricing will not find it here. Nexusguard is a consultative purchase.
Verdict: If you need a managed partner for risky public assets, this helps you combine DDoS mitigation and application filtering under one service model.
17. Gcore DDoS Protection

Gcore is an edge, cloud, CDN, and security provider with roots in performance-heavy workloads such as media, gaming, and global application delivery. Its DDoS team emphasizes edge mitigation close to users.
Best for: gaming startups and global SaaS teams that want DDoS protection bundled with edge infrastructure.
- L3/L4 and L7 protection tiers → lets teams match network or application defense to the asset type.
- CDN and edge security coupling → saves about two vendor handoffs between performance and security operations.
- Resource-based onboarding → gives first value after DNS, proxy, or protected-resource configuration.
Pricing & limits: From custom quote/mo for protected-resource plans; trial length may be available by request; clear caps depend on resource count, selected tier, SLA, L7 inclusion, and whether extra equipment is required.
Honest drawbacks: Public pricing is not as transparent as hyperscaler entry tiers. Advanced use cases need sales sizing.
Verdict: If you already need CDN, edge, and DDoS together, this helps you simplify the performance-security stack within one vendor relationship.
18. OVHcloud Anti-DDoS
OVHcloud is a major European cloud and hosting provider known for bare metal, VPS, public cloud, and included network protection. Its infrastructure teams built Anti-DDoS into the hosting experience rather than selling it only as a premium add-on.
Best for: bare-metal customers, VPS users, and game server operators who want included network-level protection.
- Included mitigation on OVHcloud services → reduces surprise DDoS exposure for hosted servers and infrastructure.
- Edge firewall and mitigation profiles → saves about two basic network-filtering steps during repetitive attacks.
- Already-on infrastructure model → gives first value as soon as the protected service is provisioned.
Pricing & limits: From $0/mo as an included feature on eligible OVHcloud infrastructure; trial length follows the purchased hosting product; clear caps depend on service line, mitigation profile, game protection availability, edge firewall rules, and support tier.
Honest drawbacks: Included protection does not mean perfect application-layer defense. Some users still need WAF, CDN, or specialized game filtering.
Verdict: If you want affordable hosting with baseline DDoS resilience built in, this helps you reduce network-layer risk from day one.
19. Link11 DDoS Protection
Link11 is a European cybersecurity provider focused on DDoS protection, WAAP, WAF, API security, bot management, and managed edge security. Its team leans into automation, GDPR-aware operations, and unlimited DDoS protection packaging.
Best for: European ecommerce teams and regulated midmarket companies that want predictable web DDoS pricing.
- AI-powered web DDoS mitigation → blocks abusive traffic without forcing teams into usage-based attack bills.
- WAAP, WAF, API, and bot bundle paths → saves about three vendor-selection steps as security needs mature.
- Plan-based onboarding → gives first value after DNS routing and policy activation.
Pricing & limits: From €613/mo on monthly Essential pricing or €490/mo on annual Essential pricing; trial length is replaced by a 90-day money-back guarantee; clear caps include feature tier, support tier, SSO availability, API and bot modules, and enterprise DDoS scope.
Honest drawbacks: The lowest plan is still above hobbyist budgets. Buyers outside Europe should test latency and support expectations.
Verdict: If predictable pricing matters as much as mitigation, this helps you budget web DDoS defense without attack-traffic overage anxiety.
20. Corero SmartWall ONE
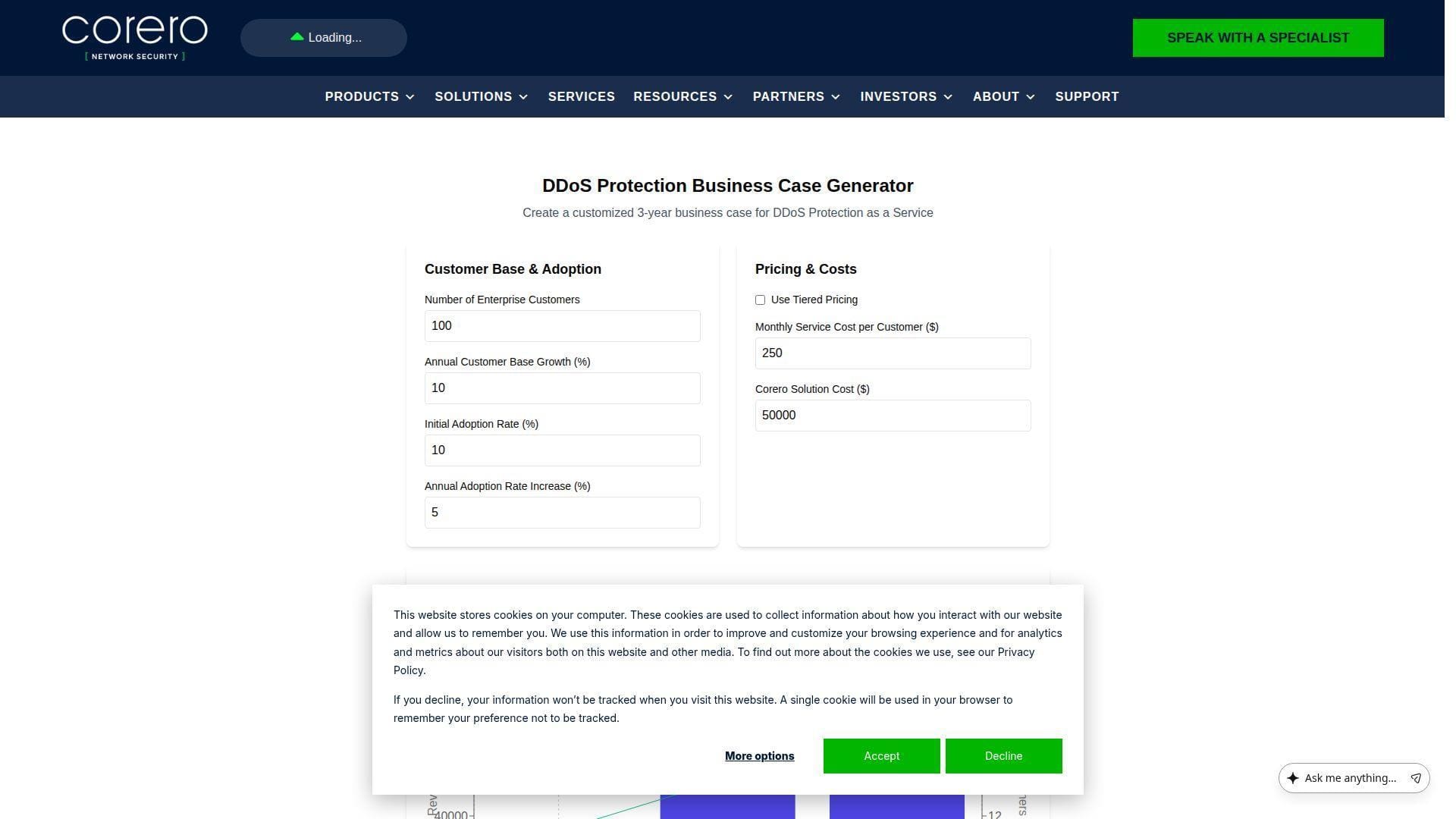
Corero specializes in real-time DDoS protection for service providers, hosting providers, and digital enterprises. SmartWall ONE reflects a team focused on inline protection, traffic visibility, automation, and fast packet-level decision-making.
Best for: ISPs, hosting providers, and infrastructure operators that need always-on inline DDoS appliances or virtual protection.
- Inline SmartWall mitigation → blocks attack packets before downstream customer infrastructure sees congestion.
- CORE visibility and managed service options → saves about one monitoring-to-mitigation handoff during live attacks.
- Appliance or virtual rollout → gives first value after network insertion, baselining, and policy validation.
Pricing & limits: From custom quote/mo; trial length is sales-led and not public self-service; clear caps depend on throughput tier, hardware or virtual model, CORE visibility, SecureWatch services, and deployment topology.
Honest drawbacks: It is built for operators, not casual site owners. You need network ownership and packet-flow visibility to get full value.
Verdict: If you operate the network edge, this helps you turn DDoS mitigation into an always-on infrastructure control instead of a panic button.
What DDoS Protection Solutions Are and Why They Matter
DDoS protection solutions detect, absorb, filter, and route attack traffic so websites, applications, APIs, and networks stay reachable. The scale is sobering: NETSCOUT described more than eight million DDoS attacks worldwide in a recent half-year threat report, which is why we treat DDoS as availability engineering, not merely security hygiene.
1. How DDoS Attacks Disrupt Websites, Applications, Servers, and Networks
A DDoS attack floods a target with traffic, requests, or protocol abuse from many sources. The victim may be a website, API, DNS service, database gateway, load balancer, firewall, VPN, game server, or entire IP range.
The disruption can happen at different bottlenecks. Volumetric floods saturate bandwidth. Protocol attacks exhaust connection tables or stateful devices. Application-layer attacks ask the server to perform expensive work that looks legitimate at first glance.
That last point matters. A simple firewall might drop obvious junk traffic. It may not understand that a login endpoint, search route, or checkout API is being abused by bots acting like impatient customers.
2. Why Uptime, Revenue, Reputation, and SLAs Depend on Mitigation
Availability is a business promise. If a store cannot process orders, the attack becomes lost revenue. If a SaaS API times out, customers file tickets and engineers burn incident hours.
For hosting providers like us, the damage can cascade. One attacked tenant can pressure shared infrastructure, upstream capacity, support queues, and customer confidence. The right mitigation keeps that blast radius small.
SLAs also change the math. A few minutes of downtime can trigger credits, contract reviews, or executive escalations. Strong DDoS mitigation gives technical teams time to act before the business relationship starts to crack.
3. Why DDoS Attacks Are Often Hard to Detect Early
Early DDoS traffic often resembles normal growth. A marketing campaign, product launch, flash sale, crawler wave, and attack can all look like sudden popularity.
The hard part is intent. A thousand users refreshing a page may be good news. A thousand bots forcing expensive cache misses may be an attack. Detection needs baselines, behavior signals, protocol awareness, and context from logs.
We prefer layered monitoring: edge analytics, server metrics, application traces, DNS visibility, and billing alerts. When those views agree, the team avoids guessing under pressure.
Types of DDoS Attacks to Match With the Right Protection
Different DDoS attacks require different controls. Buying only bandwidth does not stop application abuse. Buying only a WAF does not save a saturated network link. The best DDoS protection solutions map each asset to the attack layers that can hurt it most.
1. Application Layer Attacks
Application-layer attacks target HTTP, HTTPS, APIs, login flows, search endpoints, GraphQL routes, cart operations, and dynamic pages. They are dangerous because each request can force database reads, cache bypasses, session checks, or expensive business logic.
Radware reported that Web DDoS attacks surged 550%, and that aligns with what we see in the field: bots increasingly hide inside traffic that looks like normal user behavior.
To mitigate this class, look for WAF rules, bot management, rate limiting, JavaScript challenges, device signals, behavioral baselines, API schema controls, and cache strategy. The goal is not to block everyone. The goal is to preserve good users while making abuse expensive.
2. Protocol and Transport Layer Attacks
Protocol attacks abuse TCP, UDP, ICMP, SYN handshakes, fragmented packets, reflection vectors, and stateful middleboxes. Firewalls and load balancers often become the first weak point because they must track connections.
Transport-layer attacks are a classic reason to use upstream scrubbing. If malicious packets reach your firewall at full volume, the firewall has already become part of the bottleneck.
Strong mitigation uses stateless filtering, SYN protection, packet validation, connection-rate controls, and anycast absorption. For businesses with public IP infrastructure, this layer deserves serious attention.
3. Volumetric and Bandwidth-Saturation Attacks
Volumetric attacks are brute force. They overwhelm circuits, peering links, cloud egress paths, or network interfaces with sheer traffic volume.
Once your connection is saturated, local defenses become irrelevant. You cannot filter packets you cannot receive. This is why global capacity, upstream scrubbing, and clean-traffic delivery are essential.
Cloud scrubbing centers and large edge networks help because they absorb attack traffic near the source. The clean traffic then returns through GRE tunnels, private connections, CDN routes, or provider backbones.
4. Multivector Attacks That Shift Tactics Midattack
Modern DDoS attacks rarely stay polite. A campaign may begin as a UDP flood, shift to SYN pressure, then pivot into HTTP login abuse when network filters activate.
This tactic stresses people as much as systems. Manual rule writing cannot keep up if the attack changes every few minutes. Adaptive mitigation and prebuilt runbooks matter.
When we design for resilience, we assume shifting vectors. That means DNS readiness, WAF profiles, network filtering, origin shielding, autoscaling discipline, and clear roles before the attack begins.
Core Capabilities to Compare in DDoS Protection Solutions
A feature checklist can be misleading. The better question is operational: can the platform detect the attack quickly, filter accurately, preserve real users, report clearly, and avoid surprise costs? That is where strong DDoS protection solutions separate themselves.
1. Global Network Capacity and Scrubbing Reach
Capacity is not only a marketing number. It determines whether the provider can absorb regional floods without shifting pain to the customer.
Scrubbing reach matters too. If mitigation happens far from the attack source or user population, latency rises and legitimate traffic suffers. Anycast networks, regional scrubbing centers, and strong peering can reduce that penalty.
For global businesses, we recommend testing routes from the regions that matter most. A provider can look impressive on paper and still underperform for a specific user base.
2. Real-Time Detection, Adaptive Mitigation, and Automation
DDoS attacks can finish before a human approves a change. Real-time detection is table stakes. Adaptive mitigation is the next layer.
Look for systems that learn normal traffic, detect anomalies, create temporary rules, and roll back safely. Automation should reduce toil, not create mysterious blocks.
We like platforms that expose why a rule fired. If operators cannot explain the mitigation, they cannot defend it during a customer escalation.
3. Layer 3, Layer 4, and Layer 7 Coverage
Layer coverage should match your exposed assets. Public IP ranges need network and transport protection. Websites and APIs need application controls.
A CDN-only plan may help a website but leave game servers, VPNs, mail gateways, or custom TCP services exposed. A network scrubbing plan may protect bandwidth but miss nuanced bot behavior.
The strongest designs blend layers. We call this defense by choke point: stop bad packets upstream, stop abusive sessions at the edge, and stop expensive business logic inside the app.
4. Bot Management, WAF, Rate Limiting, and Challenge Mechanisms
Application-layer DDoS often overlaps with bots. The same machinery used for scraping, credential stuffing, and inventory hoarding can become a denial-of-service tool.
WAF rules help with known exploit patterns. Rate limits help with repetition. Bot management helps with behavior and identity. Challenges help when confidence is uncertain.
The trick is calibration. A challenge that saves the server but blocks paying customers is not a win. We prefer progressive friction: allow, rate-limit, challenge, block, and review.
5. Analytics, Reporting, and Post-Attack Visibility
After an attack, leadership asks simple questions: what happened, what was affected, what did we block, and what should change?
Good reporting answers those questions with timelines, vectors, top sources, mitigated volume, false-positive indicators, and recommended policy changes. Poor reporting leaves teams with screenshots and guesswork.
For providers and agencies, reports also build trust. A customer may forgive an incident if the explanation is clear, factual, and followed by visible hardening.
Deployment Models for DDoS Protection
Deployment model shapes latency, control, cost, and failure mode. We do not believe there is one universal model. The right choice depends on assets, traffic patterns, compliance, team skill, and how fast you must mitigate.
1. Always-On Cloud Mitigation
Always-on cloud mitigation routes traffic through the provider continuously. This works well for websites, APIs, and businesses that want fast automatic response.
The benefit is consistency. Traffic is already flowing through the defense layer, so there is no panic reroute during an attack. Baselines are also richer because the provider sees normal traffic.
The trade-off is dependency. You must trust the provider’s routing, TLS handling, policy engine, and support quality every day, not just during emergencies.
2. On-Demand Scrubbing and Traffic Diversion
On-demand scrubbing keeps normal traffic on your usual path until an attack triggers diversion. This often uses BGP, DNS, GRE tunnels, or provider-assisted route changes.
The benefit is reduced day-to-day routing change. Some enterprises prefer this because it preserves existing network paths in peacetime.
The risk is activation time. If the attack is short and sharp, the business may feel the outage before the diversion finishes. Rehearsals are mandatory.
3. On-Premises Appliances and Virtual Appliances
On-premises appliances sit near the network edge and inspect traffic locally. They are valuable for state-exhaustion attacks, internal visibility, and service-provider environments.
Appliances can act quickly because they see packets before firewalls or customer segments collapse. Virtual appliances add flexibility for cloud and NFV environments.
However, local devices cannot absorb more bandwidth than the upstream link delivers. For big floods, they need cloud scrubbing or upstream cooperation.
4. Hybrid DDoS Protection for Cloud and Data Center Environments
Hybrid DDoS protection combines local detection and cloud-scale absorption. We like it for serious infrastructure because it balances speed and capacity.
Local systems catch smaller, targeted, or stateful attacks quickly. Cloud scrubbing handles the flood when the pipe is at risk. Automation links the two.
The challenge is choreography. Routing, thresholds, tunnels, support contacts, and rollback steps must be tested. A hybrid design that exists only on paper will fail when stress arrives.
How DDoS Mitigation Works From Detection to Recovery

DDoS mitigation is a lifecycle, not a magic switch. The flow usually moves from baseline to detection, then absorption, filtering, clean delivery, validation, reporting, and policy tuning. Skipping any stage leaves blind spots.
1. Traffic Baseline and Anomaly Detection
A baseline defines normal. It captures ordinary request rates, packet mix, geographies, protocols, cache behavior, user agents, and endpoint patterns.
Without a baseline, teams guess. With one, unusual behavior becomes visible faster. For example, a sudden rise in cache-miss POST requests to a costly endpoint can stand out before servers fall over.
Baselines should evolve. Product launches, campaigns, seasonal demand, and new regions all change normal traffic.
2. Attack Response, Absorption, and Diversion
Once detection triggers, the provider or internal team decides how to respond. Always-on platforms may start filtering immediately. On-demand models may divert traffic into scrubbing.
Absorption happens at the edge or scrubbing center. The attacker’s volume meets a larger network, so your origin does not carry the full load.
Diversion must be clean. Misconfigured tunnels, DNS TTLs, asymmetric routing, or origin exposure can turn mitigation into another outage.
3. Filtering, Scrubbing, and Clean Traffic Delivery
Scrubbing separates malicious traffic from legitimate traffic. At network layers, this may involve packet validation, protocol checks, and rate controls. At application layers, it may involve WAF rules, bot scoring, challenges, and behavioral analysis.
Clean traffic then returns to the origin, data center, cloud load balancer, or application gateway. Ideally, users notice little or nothing.
False positives are the danger. If mitigation blocks real customers, the business still loses. We therefore value staged policies and fast rollback.
4. Post-Attack Analysis and Rule Tuning
Recovery begins after traffic normalizes. The team should review what triggered, what blocked, what leaked through, and what confused operators.
Good post-attack work improves future response. It may change rate limits, cache rules, origin exposure, DNS architecture, alert thresholds, or escalation paths.
We also recommend a business-facing summary. Executives do not need packet dumps. They need impact, response, residual risk, and next steps.
How to Choose the Best DDoS Protection Solution
The best DDoS protection solution is the one that matches your assets, risk, team, and budget. A small WordPress site, a payment API, a game server, and a regional bank do not need the same architecture.
1. Match Protection Layers to Your Assets and Attack Risk
Start with an asset inventory. List domains, APIs, IPs, DNS zones, load balancers, VPNs, game servers, admin panels, and third-party dependencies.
Then map each asset to likely attack layers. Websites need WAF, CDN, bot controls, and L7 DDoS handling. Public IP services need L3/L4 coverage. DNS needs authoritative resilience.
Do not protect only the homepage. Attackers often choose the forgotten endpoint because it is cheaper to break.
2. Compare Mitigation Capacity, Latency, and Global Coverage
Capacity answers whether the provider can absorb. Latency answers whether users can still tolerate the protected path. Coverage answers whether protection exists near your users and likely attack sources.
Ask vendors how clean traffic returns. GRE, proxy, CDN, private interconnect, and native cloud routing all behave differently.
Test before buying if possible. Synthetic benchmarks are useful, but real user regions and real application paths tell the better story.
3. Evaluate Automation, SLAs, Support, and Managed Response
During an attack, support quality becomes part of the product. A fast portal is helpful. A skilled response team is better.
Look for clear time-to-mitigate language, escalation paths, incident contacts, runbook collaboration, and post-attack reports. If the vendor cannot explain their response model, pause.
Automation should be transparent. We prefer systems that show active rules, mitigation reason, affected traffic, and confidence levels.
4. Check Cloud, CDN, WAF, DNS, and SIEM Integrations
DDoS defense is stronger when it integrates with the rest of the stack. CDN and WAF integrations reduce origin load. DNS integrations make failover cleaner. SIEM integrations keep security teams informed.
Cloud-native tools are compelling when your workloads live in one cloud. Cloud-neutral tools shine when you run hybrid or multi-cloud.
For 1Byte customers, we also look at hosting architecture. A protected domain still needs secure origin configuration, SSL, sensible firewall rules, and resource headroom.
5. Consider Pricing Based on Clean Traffic, Protected Resources, and Attack Overages
DDoS pricing can be deceptively complex. Some providers charge by protected IP, others by domain, request volume, clean traffic, bandwidth, subscription tier, or enterprise contract.
Ask one plain question: what happens to the bill during an attack? The wrong answer can turn a security incident into a finance incident.
Also check what is excluded. Bot management, advanced WAF, logs, SIEM export, emergency response, and support may sit outside the base plan.
DDoS Protection Readiness Checklist Before an Attack
Readiness beats heroics. We have seen teams buy protection during an incident, only to lose time on DNS, certificates, routing, ownership, and billing approval. Prepare while traffic is calm.
1. Identify Normal Traffic Patterns
Capture ordinary traffic by hour, day, region, endpoint, protocol, and user type. This helps teams distinguish a real campaign from an attack.
Include business context. A sale, livestream, exam window, or product release can look abnormal to machines. Security and marketing should talk before traffic spikes.
Store baselines where operators can find them. A dashboard no one opens during incidents is theater.
2. Inventory Critical Systems
Document domains, DNS providers, SSL certificates, origins, public IPs, load balancers, databases, admin tools, and third-party APIs. Include owners and escalation contacts.
Rank systems by business impact. Checkout, login, DNS, support portals, and payment callbacks often deserve higher protection than brochure pages.
Inventory also reveals hidden exposure. We often find old staging hosts, direct origin IPs, and forgotten admin paths during this exercise.
3. Define Mitigation Time Targets and Response Roles
Decide what “fast enough” means before the attack. A content site, bank API, and game server have different tolerance.
Assign roles. Someone owns vendor contact, someone owns DNS, someone owns application logs, someone owns customer communication, and someone owns executive updates.
Ambiguity wastes minutes. In DDoS response, minutes are not small change.
4. Deploy Protection Before Traffic Spikes Become Incidents
Do not wait for attackers to teach the architecture. Deploy the protection path, validate SSL, test origin locking, and confirm clean traffic behavior.
For on-demand scrubbing, run route exercises. For CDN or WAF protection, confirm the origin cannot be reached directly unless that is intentional.
For cloud-native protection, verify logging and alerts. A mitigation you cannot observe is hard to trust.
5. Review Logs, Lessons Learned, and Threat Intelligence
After every abnormal event, review logs. Look for top source networks, targeted endpoints, user-agent patterns, protocol vectors, and business impact.
Feed lessons back into rules and runbooks. This is how a company moves from reactive defense to operational muscle memory.
Threat intelligence also matters. If your industry is being targeted, you want to know before your dashboard turns red.
FAQ About DDoS Protection Solutions

These questions come up often when customers compare DDoS protection solutions. Our answers are practical rather than academic, because the buying decision usually touches security, finance, engineering, and customer experience.
1. What Is the Best Protection Against DDoS Attacks?
The best protection is layered. Use upstream network mitigation for bandwidth and protocol floods, WAF and bot controls for application attacks, resilient DNS, origin shielding, logging, and a tested response plan.
For a small website, Cloudflare-style edge protection may be enough. For a public IP network or gaming platform, dedicated scrubbing or provider-level anti-DDoS becomes much more important.
2. What Are the Best DDoS Protection Services?
For websites and SaaS, we would shortlist Cloudflare, Fastly, Imperva, Akamai, Google Cloud Armor, AWS Shield, and Azure DDoS Protection depending on cloud stack. For carrier and infrastructure-heavy use, Radware, NETSCOUT Arbor Cloud, A10, F5, Corero, Nexusguard, Link11, Gcore, and OVHcloud deserve attention.
The best service is not always the biggest brand. It is the one that fits your traffic, team skill, budget, compliance, and deployment model.
3. Who Is the Leader in DDoS Protection?
There is no single leader for every architecture. Cloudflare leads many web-first conversations. Akamai Prolexic is strong in enterprise scrubbing. NETSCOUT and A10 are serious choices for networks and service providers. AWS, Azure, and Google are compelling for workloads already inside their clouds.
We advise buyers to avoid trophy purchasing. Choose the leader for your use case, not the loudest logo.
4. Are DDoS Attacks Illegal in the United States?
Yes. In the United States, unauthorized actions that impair protected computers can fall under 18 U.S.C. § 1030, commonly associated with the Computer Fraud and Abuse Act.
Do not “test” someone else’s site, server, API, or network without written authorization. Even a short attack can cause real damage and legal exposure.
5. Can a Firewall Stop a DDoS Attack?
A firewall can stop some bad traffic, but it is rarely enough by itself. Many firewalls are stateful, which means they can become exhausted during floods.
Firewalls also sit too close to the protected infrastructure. If the upstream link is saturated, the firewall never gets a fair chance.
Use firewalls as one layer. Pair them with upstream mitigation, WAF rules, rate limits, bot controls, and proper network architecture.
6. How Do DDoS Protection Solutions Handle Legitimate Traffic During an Attack?
They classify traffic. At network layers, they inspect packets, protocols, rates, and source behavior. At application layers, they inspect request patterns, paths, headers, sessions, reputation, and browser behavior.
Good platforms use graduated responses. They may allow trusted traffic, rate-limit suspicious clients, challenge uncertain visitors, and block obvious abuse.
This is why tuning matters. Overblocking is just another form of downtime.
7. Do Small Businesses Need DDoS Protection?
Yes, but not every small business needs an enterprise scrubbing contract. A small website should at least use reputable DNS, CDN, SSL, WAF basics, backups, monitoring, and hosting with sensible network protection.
The risk is not only being directly targeted. Opportunistic botnets, plugin abuse, fake crawlers, and attacks on shared infrastructure can still hurt a small site.
Our rule is simple: if your website generates leads, sales, support requests, or trust, it deserves baseline DDoS protection.
How 1Byte Helps Customers Build More Resilient Hosting Foundations
We cannot promise that any single hosting provider, WAF, or cloud service will make a business invincible. What we can do is help customers build cleaner foundations: safer domain launches, SSL coverage, better hosting choices, scalable cloud infrastructure, and practical guidance before traffic pressure becomes a crisis.
1. Domain Registration and SSL Certificates for Safer Website Launches
A resilient website starts before the first visitor arrives. Domain registration, DNS hygiene, and SSL certificate management define how users reach the site and how securely browsers connect.
As 1Byte, we encourage customers to treat DNS and SSL as production assets. Keep registrar access protected, use strong account security, renew certificates before deadlines, and avoid exposing unnecessary origin details.
This does not replace DDoS protection solutions. It supports them. A protected edge works better when domains, certificates, and origin rules are not chaotic.
2. WordPress Hosting, Shared Hosting, and Cloud Hosting for a Reliable Online Presence
Different websites need different hosting foundations. A small brochure site may do well on shared hosting. A growing WordPress store may need optimized WordPress hosting. A business application may need cloud hosting with more control.
We look at traffic patterns, plugin behavior, caching, database load, and security posture. Many “DDoS problems” become worse because the origin is already fragile under normal traffic.
Good hosting gives DDoS protection room to work. Caching, resource isolation, updated software, secure admin access, and monitoring can turn a scary spike into a manageable event.
Leverage 1Byte’s strong cloud computing expertise to boost your business in a big way
1Byte provides complete domain registration services that include dedicated support staff, educated customer care, reasonable costs, as well as a domain price search tool.
Elevate your online security with 1Byte's SSL Service. Unparalleled protection, seamless integration, and peace of mind for your digital journey.
No matter the cloud server package you pick, you can rely on 1Byte for dependability, privacy, security, and a stress-free experience that is essential for successful businesses.
Choosing us as your shared hosting provider allows you to get excellent value for your money while enjoying the same level of quality and functionality as more expensive options.
Through highly flexible programs, 1Byte's cutting-edge cloud hosting gives great solutions to small and medium-sized businesses faster, more securely, and at reduced costs.
Stay ahead of the competition with 1Byte's innovative WordPress hosting services. Our feature-rich plans and unmatched reliability ensure your website stands out and delivers an unforgettable user experience.
As an official AWS Partner, one of our primary responsibilities is to assist businesses in modernizing their operations and make the most of their journeys to the cloud with AWS.
3. Cloud Servers and AWS Partner Expertise for Scalable Infrastructure
For customers who need more control, cloud servers provide a stronger base for custom applications, APIs, staging environments, and scalable services. Architecture choices matter: public exposure, firewall rules, load balancing, backups, and monitoring all shape resilience.
Our AWS Partner experience also helps customers think clearly about cloud-native security. AWS Shield, WAF, CloudFront, Route 53, load balancing, and logging should not be stitched together after an incident. They should be designed as a system.
If you are unsure where to begin, start with a simple next step: list your public domains, public IPs, hosting plans, DNS providers, and most important user journeys. Then ask which one would hurt most if it disappeared for an hour. That answer tells us where to strengthen first.

