Upon activation of an SSL order with the CSR code and completion of all validation requirements, the SSL certificate will be issued and sent to your administrative contact email address. Additionally, you can download the SSL certificate from your 1Byte account. Once the SSL certificate is received, you can begin the installation process.
Zimbra mail server supports two possible ways of SSL installation:
SSL certificate installation via Zimbra Administration Console
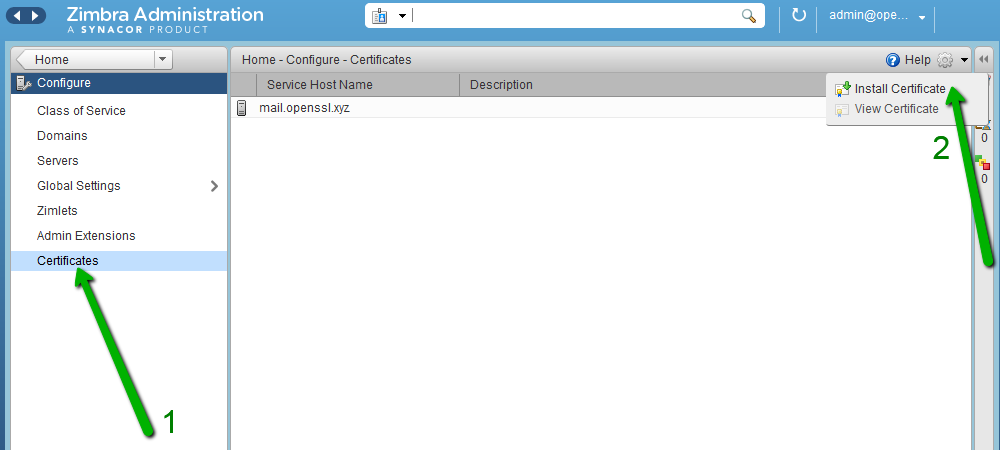
1) Click Configure in the left-hand pane of the main menu:
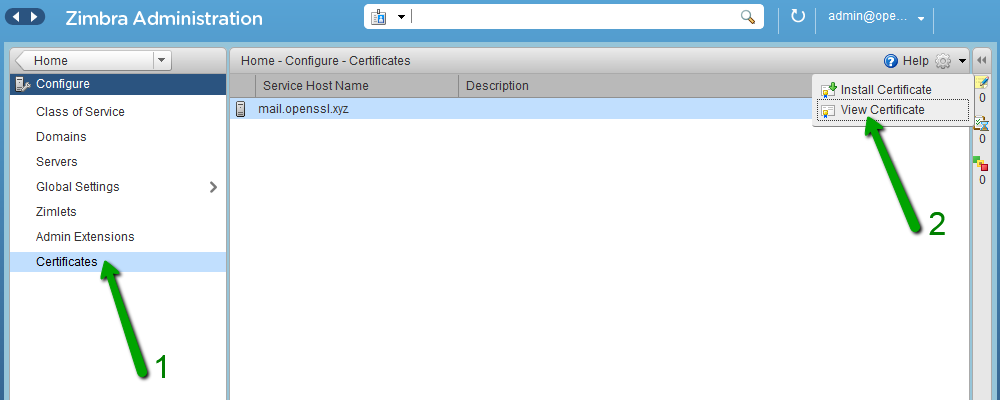
2) In the next window, click Certificates and pick up Install Certificate:
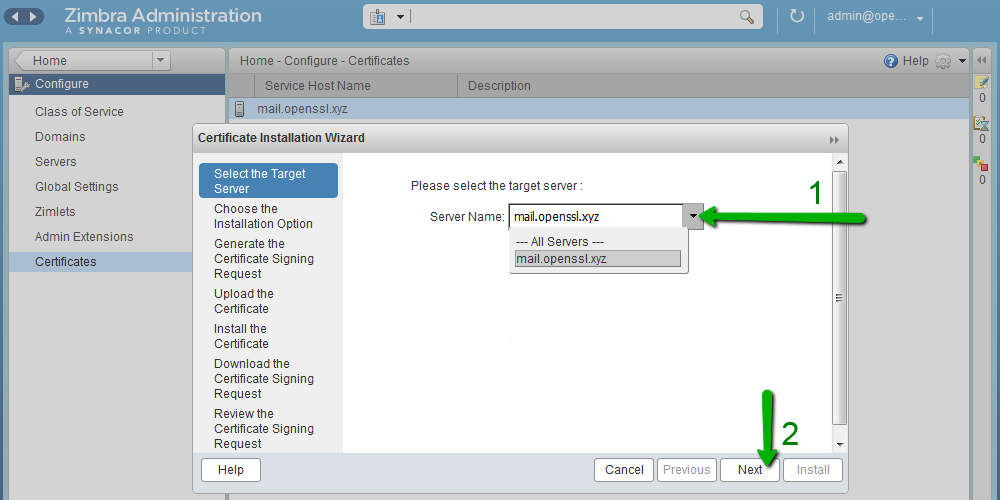
3) You will see a separate window where you need to choose the required mail server. Click Next afterwards:
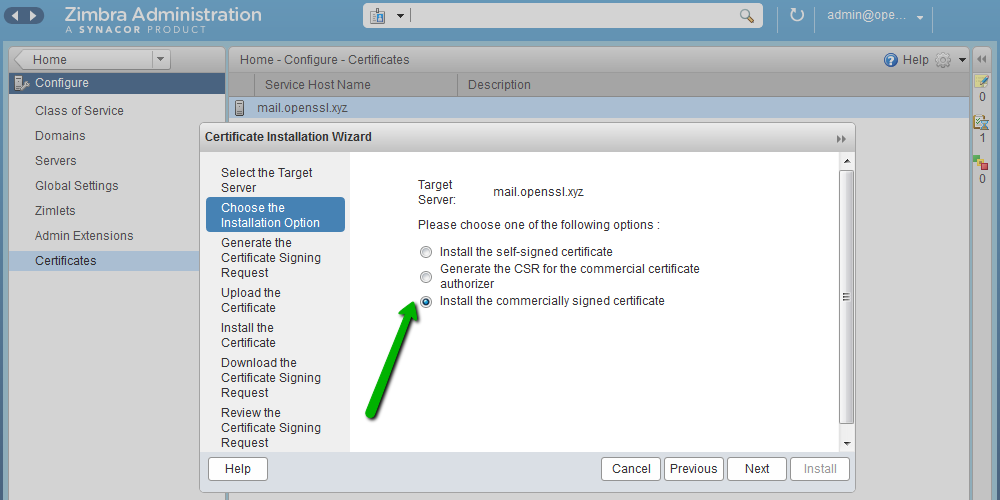
4) Pick Install the commercially signed certificate to start the installation process:
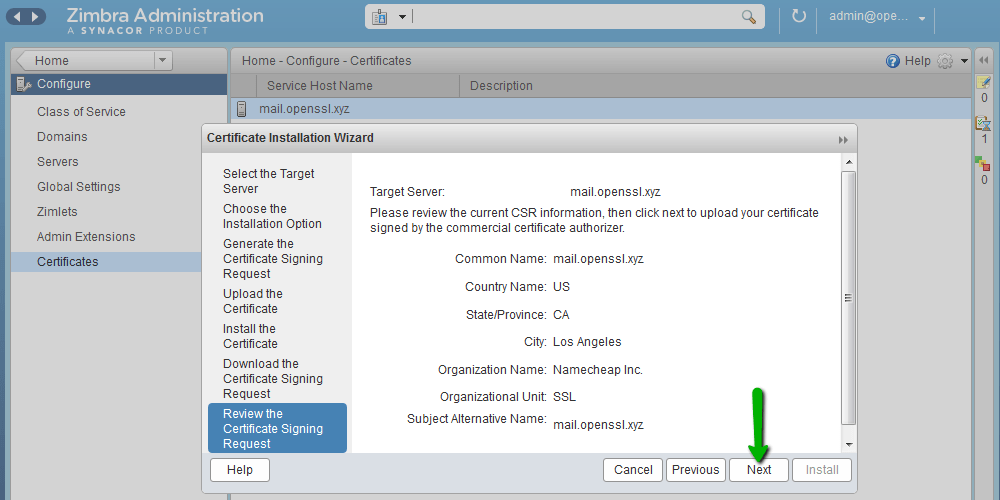
5) Review all information that was used for CSR generation. If the information is correct, click Next:
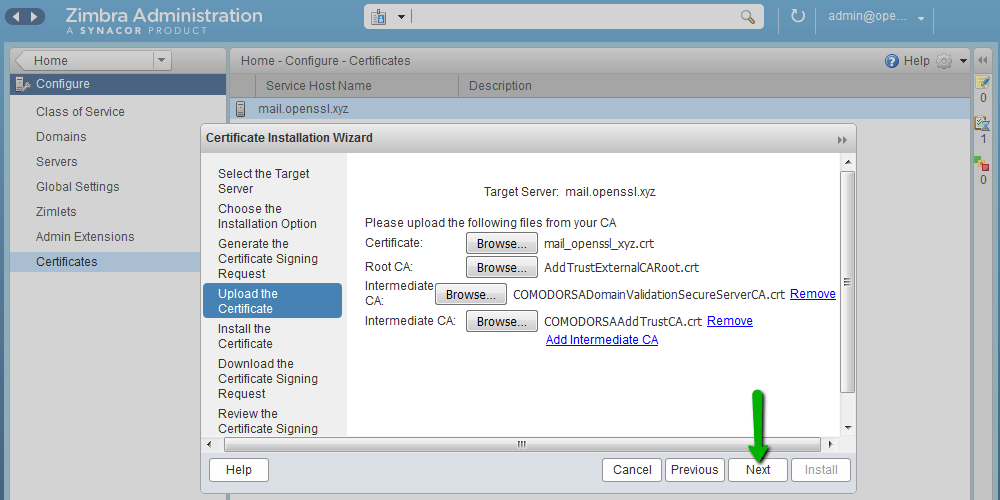
6) Upload the SSL certificate file, root certificate and intermediate certificates received from the Certificate Authority.
You can also download them, as well as your server certificate, from your 1Byte account. The root and intermediate certificates will be in the .ca-bundle file. Save them in separate files using any plain text editor (e.g., Notepad or TextEdit). The first and the second certificates in the file are intermediate certificates, and the last one is the root certificate.
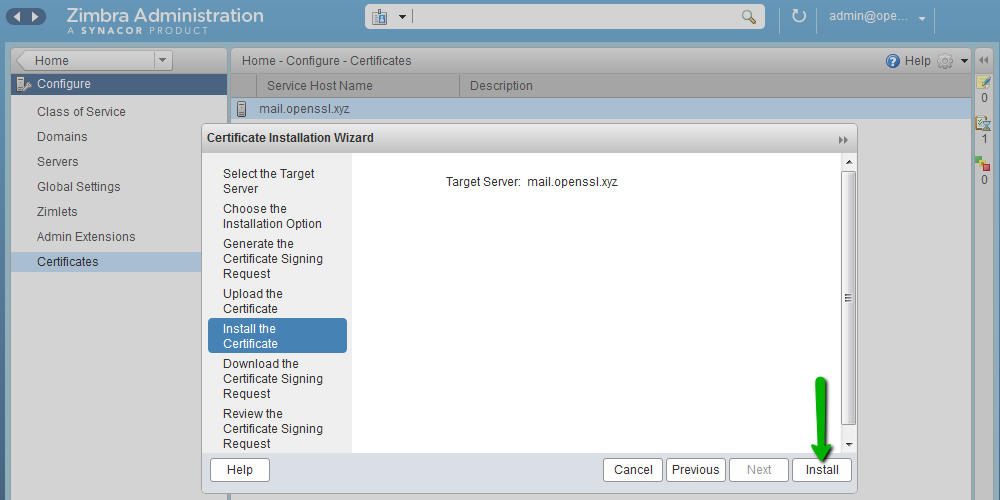
7) On the next step, click Install to install the chosen SSL certificate. The installation process can take a few minutes:
8) When the SSL installation process is completed, you will see the notification:
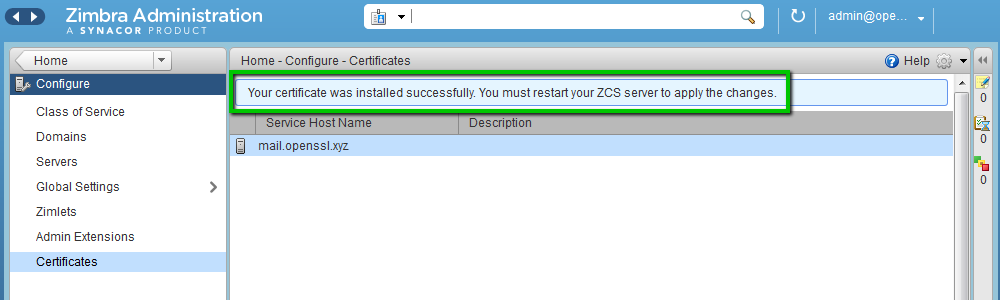
9) To apply changes, you need to restart Zimbra services like zimbra user in a CLI session:
sudo su
su zimbra
Once the default user is switched to the zimbra user, run this command to restart services:
zmcontrol restart
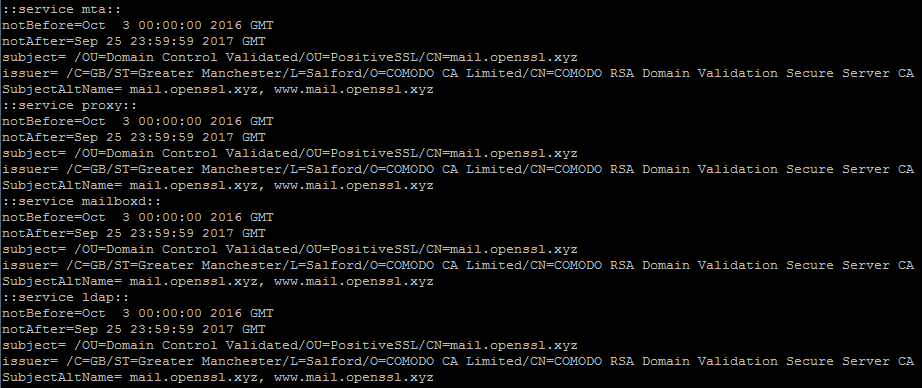
10) When all services are restarted, new SSL certificate details can checked here:
The SSL certificate has been successfully installed for the following services:
LDAP service: port 389
Mailbox service: ports 8443, 7071
MTA service: ports 25 (SMTP TLS), 465 (SMTP SSL), 7110 (POP3 TLS), 7143 (IMAP TLS), 7993 (IMAP SSL), 7995 (POP3 SSL)
Proxy service: 443, 110 (POP3 TLS), 143 (IMAP TLS), 993 (IMAP SSL), 995 (POP3 SSL).
It is possible to check SSL installation by using this online tool: https://decoder.link/sslchecker/.
SSL certificate installation via Zimbra Certificate Manager (command line interface)
A Zimbra package has the zmcertmgr tool to manage SSL certificates.
For version 8.6 or lower, this tool must be run as root. Run this command in the terminal to switch from the default user to the root:
sudo su
Starting from version 8.7 this tool should be run as zimbra user.
Run these commands to switch from the default user to the zimbra user:
sudo su
su zimbra
1) To start the installation process, you need to upload the SSL certificate file (server_domain_com.crt) and CA bundle file (server_domain_com.ca-bundle) to any folder to your hosting server on the temporary basis. For this example, SSL files have been uploaded to the /opt/ directory.
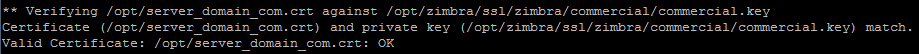
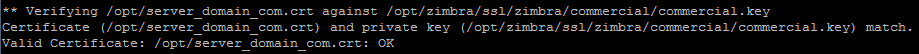
2) Verify that your certificate received from the Certificate Authority matches the private key generated along with the CSR: /opt/zimbra/bin/zmcertmgr verifycrt comm
/opt/zimbra/ssl/zimbra/commercial/commercial.key /opt/server_domain_com.crt /opt/server_domain_com.ca-bundle
The output should look like:
You can also download them, as well as your server certificate, from your 1Byte account. The root and intermediate certificates will be in the .ca-bundle file. Save them in separate files using any plain text editor (e.g., Notepad or TextEdit). The first and the second certificates in the file are intermediate certificates, and the last one is the root certificate.
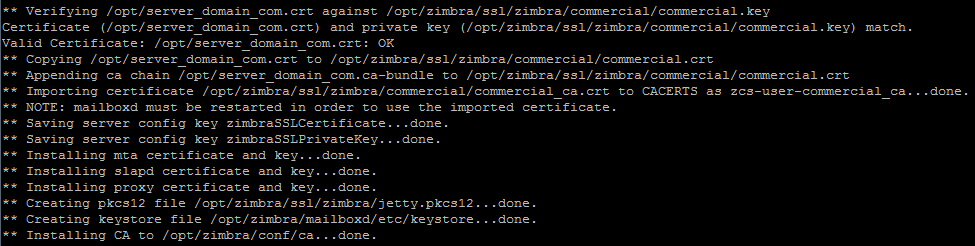
3) Deploy your commercial certificate.
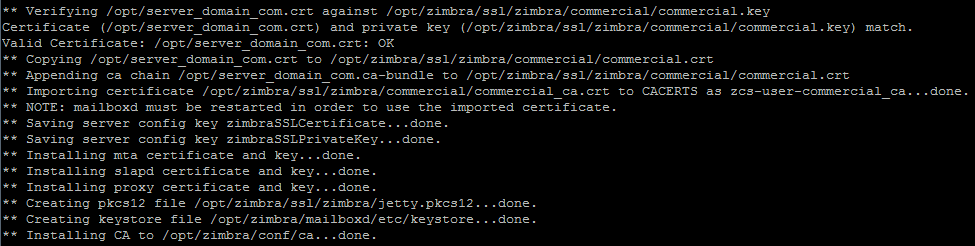
/opt/zimbra/bin/zmcertmgr deploycrt comm /opt/server_domain_com.crt /opt/server_domain_com.ca-bundle
The successful output should look like:
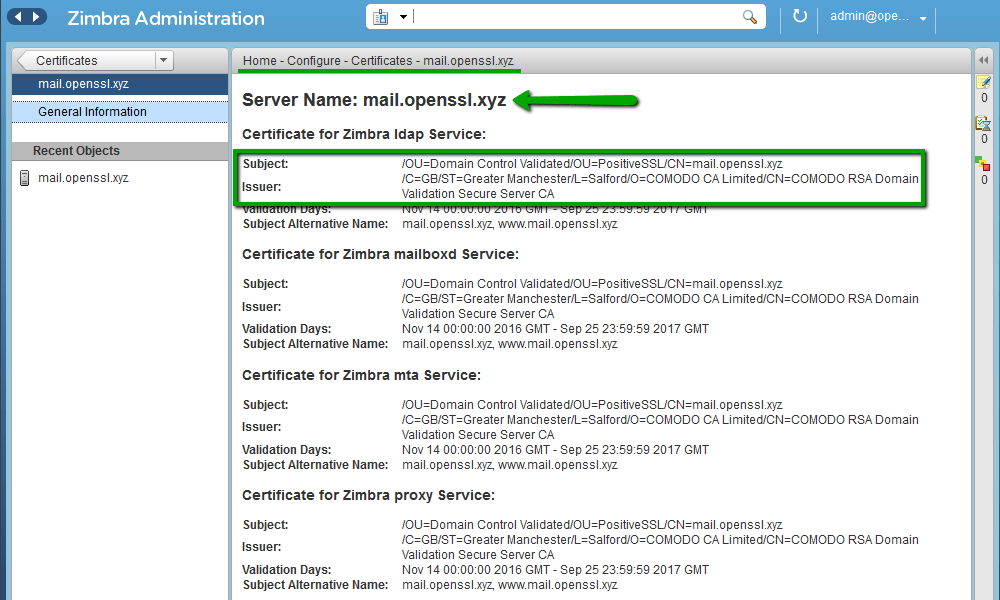
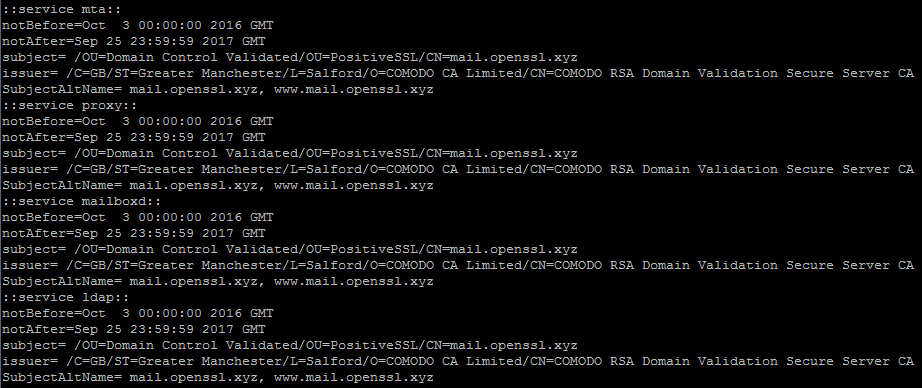
4) Verify that the correct certificate has been deployed.
/opt/zimbra/bin/zmcertmgr viewdeployedcrt
For example, the details of the PositiveSSL certificate will look like:
5) To apply changes, you need to restart Zimbra services like zimbra user:
sudo su
su zimbra
Once the default user is switched to zimbra user, run this command to restart services:
zmcontrol restart
When all services are restarted, new SSL certificate details can checked by using SSL checker tool.
How to deploy a Multi-Domain SSL certificate or SSL Wildcard certificate installed on another hosting server for Zimbra?
1) Copy the SSL certificate file (server_domain_com.crt), CA bundle file (server_domain_com.ca-bundle) and private key (commercial.key) to any folder of your hosting server on the temporary basis. For this example, SSL files have been uploaded to the /opt/ directory.
2) Copy the private key from the temporary location to the default folder of commercial certificates.
cp /opt/commercial.key /opt/zimbra/ssl/zimbra/commercial/
3) Set default permissions for the private key.
chmod 640 /opt/zimbra/ssl/zimbra/commercial/commercial.key
4) Verify that your certificate received from the Certificate Authority matches the private key
/opt/zimbra/bin/zmcertmgr verifycrt comm /opt/zimbra/ssl/zimbra/commercial/commercial.key /opt/server_domain_com.crt /opt/server_domain_com.ca-bundle
The output should look like:
5) Deploy your commercial certificate.
/opt/zimbra/bin/zmcertmgr deploycrt comm /opt/server_domain_com.crt /opt/server_domain_com.ca-bundle
The successful output should look like:
6) Verify that the correct certificate has been deployed.
/opt/zimbra/bin/zmcertmgr viewdeployedcrt
For example, the details of the PositiveSSL certificate will look like:
7) To apply changes, you need to restart Zimbra services like zimbra user in the terminal:
sudo su
su zimbra
Once the default user is switched to zimbra user, run this command to restart services:
zmcontrol restart
When all services are restarted, new SSL certificate details can checked by using this online tool: https://ssl-checker.1byte.com/